Windows UAC Privilege Escalation
Demonstration of how to perform Windows UAC Privilege Escalation (CVE-2019-1388). This vulnerability allows a user to escalate from a low privilege level (non-admin) to SYSTEM.
Download EXE
We’re going to use the exe that was used in the a PoC for this CVE. The exe can be downloaded here.
Walkthrough
Step 1
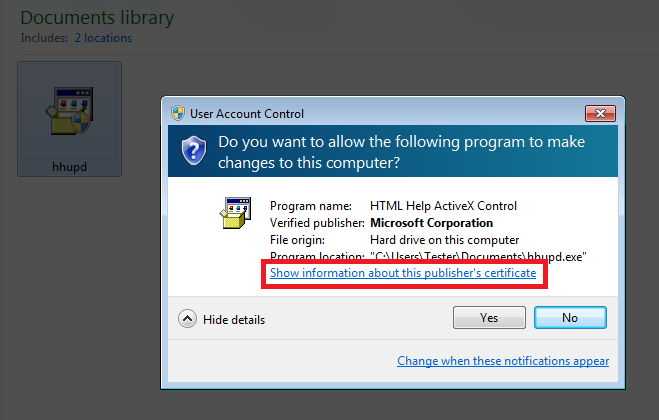
Run the program as a Admin and we should see a prompt similar to this:
Click Show details or Show more details, and click the link that says Show information about this publisher's certificate
Step 2
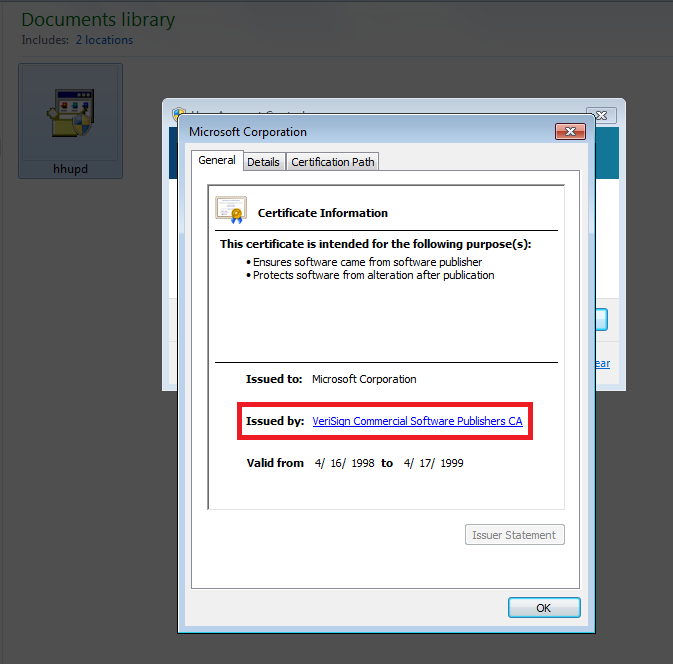
A new window will appear showing the certificate info.
In the Issued By field, click the link:
- NOTE it will appear as if nothing happened. This is normal. A browser has actually been opened that we can’t see.
Step 3
Close the window showing the certificate info, and the UAC prompt.
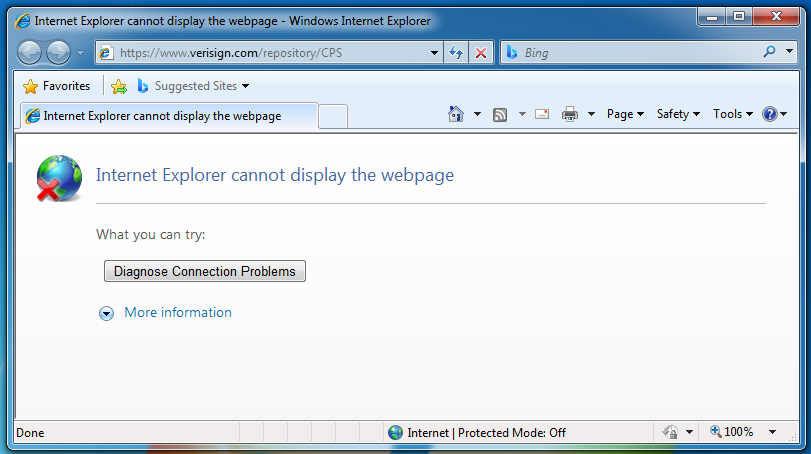
We can now see the browser that was opened:
- It doesn’t matter if the site doesn’t load. Internet is NOT required for this to work.
Step 4
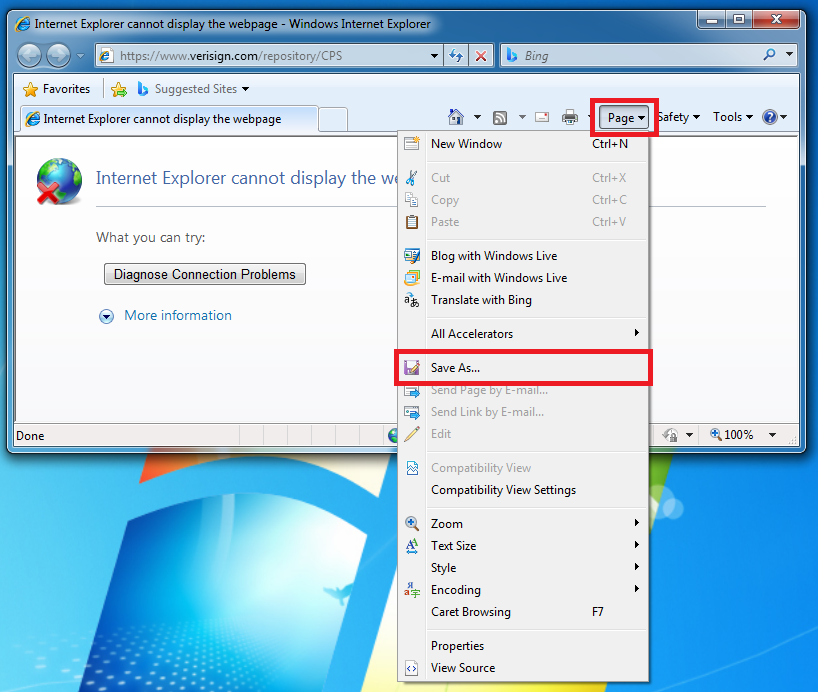
Our goal now is to open a file browser/saver window. There is a few ways we can do this.
One way is to click Page -> Save As....
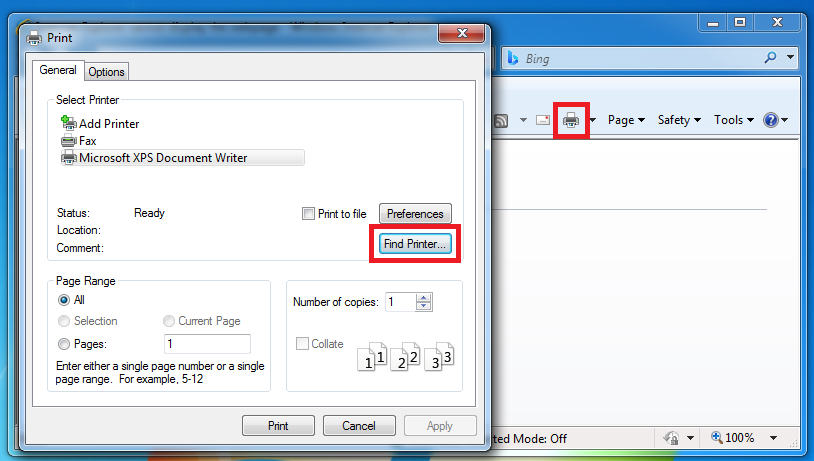
Another way is to click Print -> Find Printer.
There’s other ways to do this, choose whatever works.
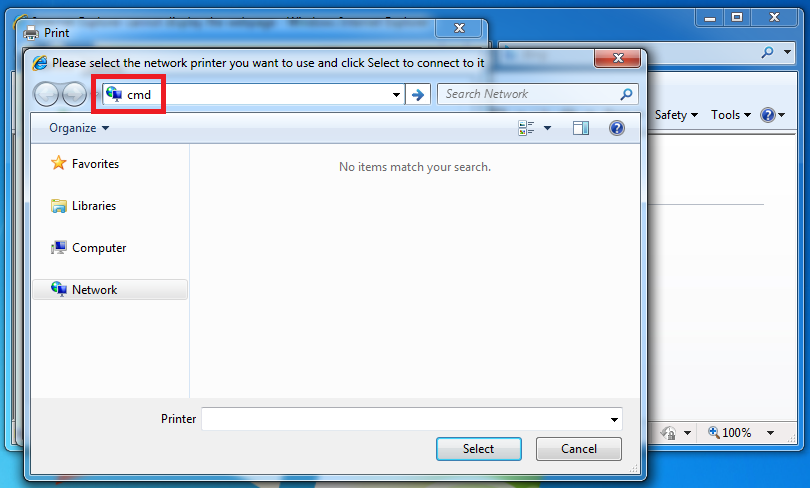
Step 5
Once we have this new window open, we need to type cmd in the location bar and click enter:
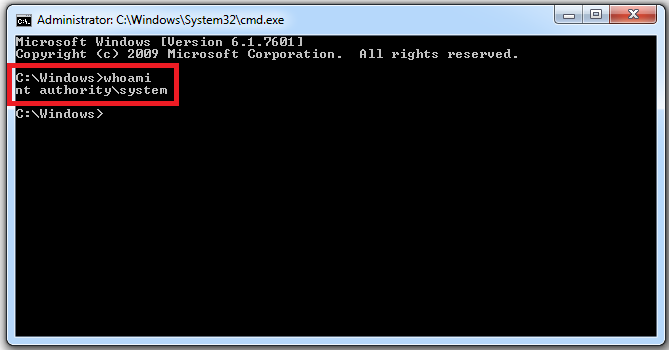
A command prompt will now open that should be running as SYSTEM: